With cyberattacks and remote workforces increasing in popularity, it’s essential to understand the differences between a secure web gateway (SWG) and a proxy server. Rather than simply delivering internet traffic to your network, a web gateway filters and blocks the web-based traffic that puts your systems at risk. An SWG enables organizations to enforce security policies and rules, blocking unwanted websites that can lead to data breaches or other threats. It also provides visibility into shadow IT and helps prevent the proliferation of malicious applications that can impact network resources.
Security
The question is, how will you differentiate secure web gateway vs proxy? Secure web gateways (SWG) are designed to protect users by preventing malicious traffic that may lead to malware infection or network intrusion. They can be software-based or hardware systems running on an organization’s premises. The most basic function of a secure web gateway is to filter user-initiated Internet traffic according to an organization’s security policy. This allows organizations to enforce acceptable usage policies and prevent data breaches from occurring on the business network. In addition to blocking unwanted content, secure web gateways can help prevent data loss by inspecting outbound Internet traffic for unique patterns and phrases matching sensitive information such as social security numbers, credit card data, medical records, and intellectual property. Some functions are built natively into secure web gateways, while others involve integration partners. Another security feature found in some secure web gateways is URL filtering. This feature uses a database of known malicious websites and website categories to keep malware at bay. It can also stop unauthorized downloads of suspicious payloads and prevent many other potential threats from entering an organization’s network. In addition to detecting and removing malware, secure web gateways can detect malicious JavaScript and cross-site scripting attacks. These attacks can inject code into vulnerable web pages and applications, allowing hackers to steal sensitive information or cause network breaches.
Performance
A Secure Web Gateway can be a good choice for organizations that want to protect their network from threats originating from the public Internet. However, security teams must ensure they don’t rely on SWGs alone to secure their networks. SWG solutions can be deployed as hardware, software, or virtual devices and may be cloud-based. Many SWGs can inspect HTTPS-encrypted traffic for malware and other malicious elements that can compromise network data integrity. The gateway can then re-encrypt the traffic and forward it to the user or web server, ensuring that sensitive information is protected from infection and theft. Another advantage of SWGs is that they provide a clearer picture of web traffic flowing through the network. This allows administrators to enforce security policies more efficiently. Some SWGs can inspect outbound traffic to identify unauthorized SaaS packages and websites. This can be an essential security tool that can prevent the loss of sensitive company data and identity theft. Many SWGs can also provide DLP functionality that can block unauthorized outbound traffic based on specific patterns or phrases that match social security numbers, credit card data, medical information, and intellectual property. This critical feature can help prevent ransomware attacks by blocking users from downloading malicious software.
Flexibility
A Secure Web Gateway is a security solution that stops unauthorized internet traffic from entering a company’s network. It also controls inappropriate websites and content and enforces security policies to protect sensitive data. The gateway can be deployed as a virtual appliance, on-premises, or in the cloud. It can secure all of the organization’s network traffic or target specific areas requiring a more granular protection level. Typically, the gateway inspects all incoming traffic before sending it to users’ browsers. It compares it to a list of acceptable use policies or security rules and passes it along if it does not violate them. Many gateways also use URL filtering to block specific website categories and known malicious sites. This prevents the download of malicious payloads and keeps malware at bay. Some secure web gateways also employ sandboxing to test suspicious code for negative behavior before it is delivered to users. It can also detect malware in an emulated environment and prevent it from executing on the user’s device. The flexibility of secure web gateways can be a tremendous asset to organizations. They help streamline security processes, improve efficiency, and provide a unified platform to manage your security policy for all device users.
Cost
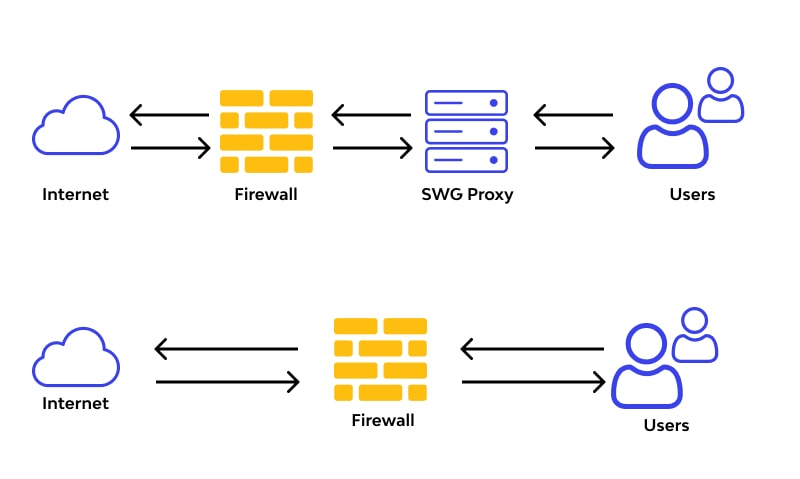
A Secure Web Gateway is a tool that allows an organization to monitor web traffic while enforcing corporate and regulatory policies. It helps businesses protect their infrastructure from malware infections and data breaches by analyzing inbound and outbound web traffic and blocking malicious applications, websites, and internet traffic not authorized to enter the network. SWG solutions can be deployed as hardware, software, or virtual appliances. They can be active along the organization’s network perimeter, or they can be located in the cloud. In either case, SWGs work as a proxy between internal users and the Internet.
In the same way that a security guard inspects a person’s possessions at a physical checkpoint before allowing them to move on to the next step, an SWG analyzes incoming and outgoing traffic from user devices, comparing it against security policies. SWGs can use URL filtering to block access to malicious sites based on URL category, user, group, or a machine to keep malicious web content at bay. Some also employ emulation to run a copy of suspicious websites in the gateway’s emulated environment, effectively identifying and detecting malware. With a secure web gateway, IT teams can eliminate the cost and complexity of purchasing and maintaining multiple redundant appliances that must be installed, configured, and replaced every three years. Furthermore, they can quickly scale the solution to large networks with little additional capital or operational expense.